Written collaboratively by Xufei Yang, former Assistant Professor & SDSU Extension Environmental Quality Engineer; Ali Mirzakhani Nafchi; Jameson Brennan; Sushant Mehan; Logan Vandermark; Sarah Sellars; Alexander Smart; Young Chang, Department of Agricultural and Biosystems Engineering, SDSU; and Yong Wang, The Beacom College of Computer & Cyber Sciences, DSU.
Introduction
Precision agriculture emphasizes using data to make smarter farming decisions. This means collecting and analyzing different types of data and then using the results to guide farming practices. To make this process more efficient, modern farming technologies rely more on computers and the Internet—this digital aspect is known as the ‘cyber layer’ of precision agriculture. Meanwhile, the ‘physical layer’ includes farm machines and equipment. However, as farms use more digital technology, they become more vulnerable to cyber threats like hacking, data breaches, and unauthorized access. These risks can create headaches for farmers and hinder the adoption of new precision farming technologies. One major concern is the risk of unauthorized access to sensitive agricultural data. In this article, we will introduce two key security measures—Authentication and Encryption—that help protect precision agriculture systems from cyber threats and keep farm data secure.
Understanding Agricultural Data

Before we dive in, here are the different types of data used in farming:
- Farm Operation Data: Includes information on crop yields, soil health, irrigation schedules, livestock weight, and feed consumption, helping farmers make better decisions.
- Sensor and IoT (Internet of Things) Data: Comes from technology like weather stations, drones, water meters, and livestock trackers, providing real-time monitoring of farm conditions.
- Financial Data: Includes data related to all financial transactions of the farm, such as loans, debts, assets, profitability, and account balances. It contains valuable information about the financial position of the farm.
- Personal Data: Involves details about employees, customers, and other individuals connected to the farm, important for workforce management and customer relations.
These data are crucial for automating farm operations, managing finances, and maintaining business relationships. However, if stolen or hacked, they can lead to serious disruptions, financial losses, or even identity theft. Data protection is essential to keeping farms running smoothly and securely.
What is Data Authentication?
Data authentication ensures that information is real, trustworthy, and comes from the right source. It also ensures that the data has not been changed or tampered with during storage or transmission. In the digital world, authentication is widely used to protect data integrity. Below are several data authentication measures used in agriculture.
Passwords and multi-factor authentication
Today, passwords are required to verify user identity on almost all modern agricultural equipment and software. This includes farm management platforms, cloud servers, GPS-guided machinery, drones, smart controllers in livestock barns, and RFID systems. With password-based authentication, users enter a username and password to log in. The system then converts the password into a secure digital format and checks if it matches the stored record. If it does, access is granted. Using a strong password is crucial for keeping your account and data secure. However, passwords alone only prove that someone has the right login details. They do not confirm who is actually using them. Hackers who steal a password can easily access farm equipment and software, putting valuable data and operations at risk. Multi-Factor Authentication (MFA) is becoming more widely used to address this issue (Figure 1).
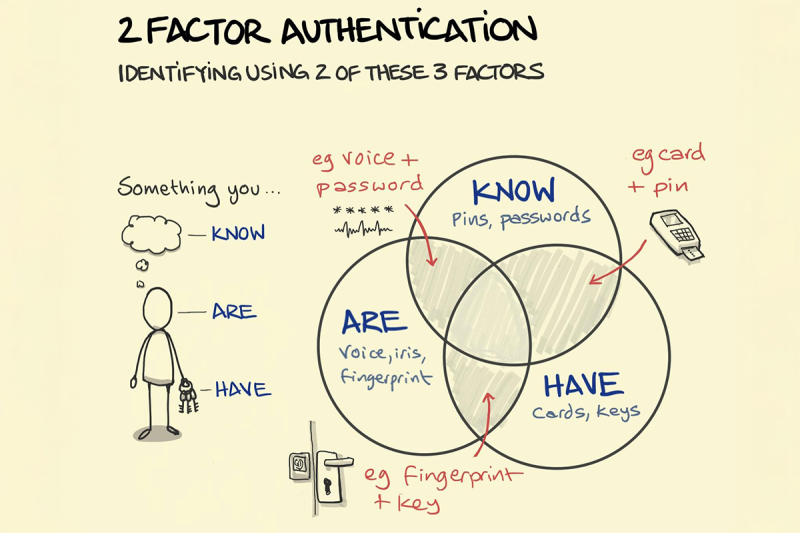
MFA is a security protocol where the user must provide two or more pieces of evidence to prove who they are when logging in. Besides your password, you might have to enter a one-time code sent to your email or phone, confirm a login request on a phone app, or use a fingerprint or face scan.
Digital signatures and certificates
A digital signature is a unique “fingerprint” code attached to data, verifying that it comes from the intended device and has not been changed. It helps protect agricultural data, prevent fraud, and ensure that farming and supply chain records remain trustworthy. The signature is created by converting the original data (including device details and readings) into a short, fixed-length code called a hash, which is then locked using a private key. When someone receives the data, they unlock the signature using a public key and compare it to a newly generated hash of the received data to ensure it matches. This makes it nearly impossible for anyone to tamper with the data without being detected.
Examples of digital signatures in agriculture include:
- Data transmission: Data from soil moisture sensors is digitally signed to ensure that farmers receive and utilize data from a trusted sensor, and no one has changed the data before it reaches them.
- Record validation: Modern farm machines can automatically keep logs of what they do, such as GPS locations and seeding rates. These records can be digitally signed to make sure no one changes them later. This helps with keeping trustworthy records and meeting regulations.
- Authentication of Ag Internet-of-Things (IoT) devices. Each device in an Ag IoT network, such as drones, weather stations, and soil sensors, is assigned a digital certificate to ensure only approved devices can connect to the network and share data. This helps keep the system secure from fake data or hackers.
- Verification of user identity. On shared agricultural data platforms, each user is given a digital certificate stored on a smart card or similar device. This helps ensure that only authorized people can access the system and makes it easier to track who does what.
A digital certificate is like an online ID card issued by a trusted organization to prove who someone or something is in a digital farming system. It includes a set of information such as the name of the person or device, a public key, who issued the certificate, when it expires, and a unique serial number. While similar to digital signatures, digital certificates involve a more complex implementation. They play a crucial role in verifying identities and ensuring that only authorized users and devices can access sensitive agricultural data.
Role-based access control (RBAC)
RBAC allows different groups of users, such as administrators, employees, or guests, to have different levels of data access in a digital farming system. This means each person can only see or do what is needed for their assigned role within an organization or supply chain, helping keep the system organized and safe. Below are some examples:
- Livestock farm management software: Workers can only see and update the information they need for their daily work, such as tracking livestock weight, feed use, health checks, and vaccinations. Only the farm owner or manager can have full access, including sensitive information such as financial data.
- Ag IoT systems: In a smart irrigation system with devices like weather stations, soil sensors, pumps, valves, and water meters all connected online, RBAC helps control who can do what. For example, only the farm manager using the office computer can issue commands or change system settings, while others can only view the data.
- Supply chains: In a meat supply chain system, people like livestock caretakers, processing plant workers, truck drivers, retailers, and inspectors each have access only to the information and tools necessary for their specific jobs. This helps ensure traceability and food safety compliance from farm to fork. For example, a retailer can see the full history of where the meat came from, but they cannot change any of the records.
What is Data Encryption?

Data encryption, a more advanced form of ‘secret code’ or ‘ciphers’, is the process of transforming data using a secret key into a coded format that no one can understand unless they have the correct key to unlock and read it. Encryption alone does not stop hackers from accessing data, but it makes the data unreadable and useless to them.
There are two main ways to keep data safe using secret keys. The first way is like using the same key to lock and unlock a door. This is called symmetric encryption, where the same secret key is used to both encrypt and decrypt the data. The second way uses two different keys: one to encrypt the data (called the public key) and another to decrypt it (called the private key). This is known as asymmetric encryption and is a bit like having a mailbox: anyone can drop a letter in (encrypt it), but only you have the key to open it (decrypt it). Both methods are widely used to keep information secure in the real world.
So, what exactly is a secret key? It is a string of letters, numbers, and/or symbols used by an encryption algorithm to transform data. Consider the algorithm as a set of rules for locking and unlocking information, and the key tells it exactly how to do that. Like a strong password, a longer and more complicated key makes it harder for someone to break in. However, stronger keys may take more time and computer power to use. Most importantly, the key must be kept secret. If hackers get access to it, they could decrypt and read your sensitive information.
Common Encryption Algorithms
For simplicity, only two commonly used encryption algorithms are discussed here:
SSL/TLS (Secure Sockets Layer/Transport Layer Security)
For instance, you have probably noticed some websites start with https:// instead of just http://. That extra “s” means the site is using SSL or TLS to keep your connection secure and protect your information as you browse. With SSL/TLS, the data transmitted between a web server, like SDSU Extension, and a browser on your computer or phone is encrypted, so that no one else can spy on what you are doing.
AES (Advanced Encryption Standard)
AES is a symmetric encryption method that uses the same key to encrypt and decrypt data. It is widely used to keep data safe during transmission between farm devices, like sensors and controllers, and their associated computers or software programs. AES works by breaking data into fixed-sized blocks and encrypting them using keys of different lengths. Like passwords, the longer the key, the stronger the protection.
Example: How AES helps keep data secure
- Imagine a soil probe in the field sends a real-time reading of “SP1 62.5 43.8%”. Here, SP1 is the sensor ID, 62.5 is the temperature in Fahrenheit, and 43.8% is the moisture content. If this information is sent as plain text, anyone can intercept and read it.
- Now, let’s use AES encryption with a secret key of “ILoveSouthDakota”. The same data is transformed into “mLgLoX5qKbn5gceFW6Lvxg==”, a scrambled message unreadable to hackers.
- If we change the secret key to “ILoveNorthDakota”, the encrypted result becomes “VXnOeQNi+smlozBaBNhW8g==”, which is completely different. This shows that the correct key is essential to unlock and read the original data.
Note: This example is created using the online AES encryption tool courtesy of Devglan.
Data Encryption Examples
Below are a few examples of data encryption in agriculture:
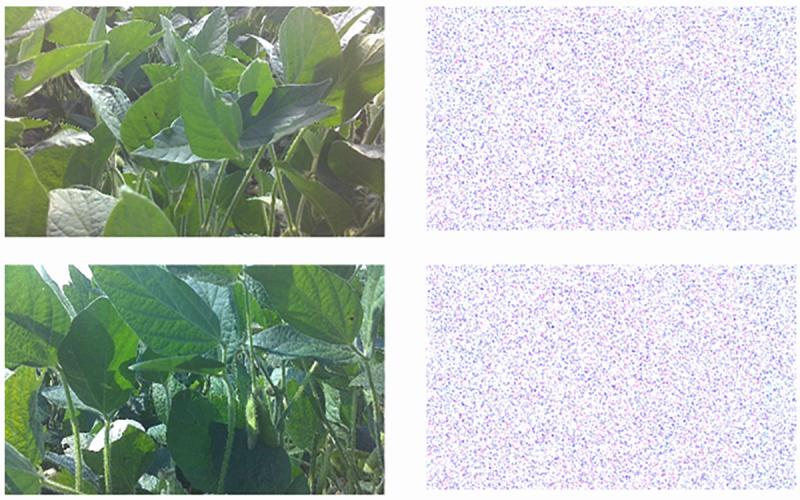
Encryption of images
Various types of cameras, such as RGB, thermal infrared, depth, multispectral, and hyperspectral, are now widely used in precision agriculture for monitoring crops and livestock. These images can show detailed information about farm conditions, which producers may want to keep private. Encrypting the images helps protect this sensitive data from unauthorized access. Figure 2 shows a comparison of two crop images before and after being encrypted using AES. The encrypted version is completely unreadable. Even if hackers can intercept the image online or steal it from a memory card, they will not be able to understand it without the correct key.
Encryption of GPS locations
GPS data plays a key role in guiding farm equipment like self-driving tractors and drones. It is important to encrypt the data to keep it safe from hackers or tampering (also known as spoofing). For example, many farms use differential or RTK GPS base stations that send highly accurate location signals to a machine like a planter in the field. These signals are often encrypted so that no one can manipulate them. This helps ensure the equipment stays on the right path.
Securing cloud-stored farm records
Farm management software often stores large amounts of sensitive information online, such as crop yields, field maps, financial records, and inventory. To protect this data from unauthorized access, cloud service providers often encrypt the data before saving it. This ensures that even if someone breaks into the cloud system, the saved data remains unreadable without the correct decryption keys. Some examples of farm management software that use encryption include Farmbrite, PickApp, and CropTracker.
Best Practices for Implementing Authentication and Encryption
In summary, authentication and encryption are two prevalent ways to keep farm data secure, accurate, and trustworthy. Authentication is used to ensure the data is real, has not been changed, and comes from a trusted source. In contrast, encryption transforms the data into a scrambled, unreadable form while it is being transmitted or stored, so no one else can understand it without the correct key(s). These two methods are often used together to enhance the overall cybersecurity of important farm data.
To effectively implement authentication and encryption, here are some easy-to-follow tips:
- Use strong, unique passwords for all your devices and accounts. Do not use the same passwords for everything and avoid easy ones like “012345” or “myfarm2025”. Enable Multi-Factor Authentication (MFA) like two-step login when you can.
- Work with trusted vendors and service providers who appreciate the importance of data security and are open about how they protect and utilize your farm information.
- Keep your device firmware and software programs up to date. These updates often aim to fix security problems, so do not ignore them.
- Make sure your sensitive data is encrypted. For instance, do not turn off its built-in security features if you are using an external hard drive.
- Teach your employees about basic cybersecurity, including how to create strong passwords, keep them safe, and use physical security tools like hardware keys when needed.
References
- Alahe, M. A., Chang, Y., Kemeshi, J., Won, K., Yang, X., & Wei, L. Real-time agricultural image encryption using Advanced Encryption Standard (AES) on edge computing devices. Computers and Electronics in Agriculture. Accepted.
- Data Security Essentials: Protecting Your Farm’s Information, Kheti Buddy.
- Ensuring Data Security and Privacy in Agricultural Management – Best Practices and Strategies, MoldStud.
- Kaur, J., Hazrati Fard, S. M., Amiri-Zarandi, M., & Dara, R. (2022). Protecting farmers' data privacy and confidentiality: Recommendations and considerations. Frontiers in Sustainable Food Systems, 6, 903230.
- Yazdinejad, A., Zolfaghari, B., Azmoodeh, A., Dehghantanha, A., Karimipour, H., Fraser, E., Green, A.G., Russell, C., & Duncan, E. (2021). A review on security of smart farming and precision agriculture: Security aspects, attacks, threats and countermeasures. Applied Sciences, 11(16), 7518.


